Bad Rabbit: Good rabbit gone bad
Here I present you our next delicious ransomware, Bad Rabbit. Bad Rabbit mostly affected Russia and Ukraine. ESET confirmed it’s spread in Japan and Bulgaria. Other sources have also reported the ransomware to be in U.S., Germany, Turkey, Poland and South Korea. The ransomware affected Ukrainian transport, especially Odessa’s airport, and the Kiev subway. The cybersecurity firm Group-IB. Confirmed the attacks on Russian media companies Interfax and Fortanka. Interfax has officially confirmed that its server had gone down; because of this ransomware.
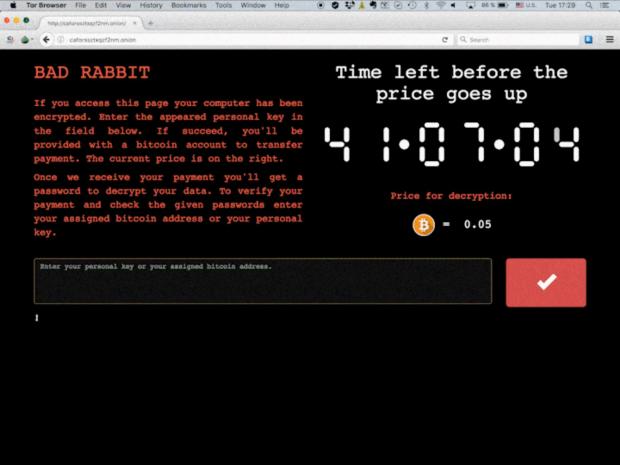
Bad Rabbit uses a popular malware trick. Posing itself as an Adobe update. Once you install the malware, it’ll lock down your computer and asks for a ransom of 0.5 bitcoins ($280). If you don’t pay it within 40 hours, the cost to free your data will increase. Unlike NotPetya, this doesn’t delete your files but damages them. Security experts advise not to pay the amount. As there is no guarantee you’ll get your data back. It doesn’t only attacks your computer but tries to get through other shared PCs.

Bad Rabbit seems like its predecessors

The seems like previous two major ransomware attacks. NotPetya and WannaCry. That caused widespread disruption in businesses, government institutions across the globe. Bad Rabbit targets corporate agencies, prompts the message in red font on a black background same as NotPetya. Bad Rabbit also uses a version of Petya ransomware, which again you guessed right. As the name suggests NotPetya also used a version of Petya. Not only that. The attack was launched through an elaborate network of hacked websites with a link to NotPetya.
Though not as bad as NotPetya or WannaCry

Before you think of this as another attack from the same person who launched NotPetya. Here’s the catch, Bad Rabbit doesn’t use EternalBlue, the Windows exploit. Leaked in a batch of hacking tools believed to belong to U.S. National Security Agency (NSA). Though this attack is not as widespread as Wanna cry and NotPetya. Here’s a tweet about some prevention you can do yourself.
I can confirm – Vaccination for #badrabbit:
Create the following files c:\windows\infpub.dat && c:\windows\cscc.dat – remove ALL PERMISSIONS (inheritance) and you are now vaccinated. 🙂 pic.twitter.com/5sXIyX3QJl— Amit Serper (@0xAmit) October 24, 2017

The attacker appears to be a fan of Game Of Thrones. There were references of Daenerys’ Dragons and Grey Worm throughout the code. The unidentified attacker is believed to out of action. There are only scripts running from the previous launches. Windows has taken the preventive measure, your Windows Defender can detect the Bad Rabbit.
Seriously, who still downloads stuff from those pop-ups. It’s more like a reflex action, pop up? CLOSE THAT SHIT!. Ads are a crucial source of income for many websites, so it can’t be totally uprooted. What are the preventive measures you think one can take to prevent things like these from happening? Comment down below!

